QuiddiKey 100
The number of connected devices, machines or sensors that are linked with each other over open communication networks on the internet of things (IoT) has exploded. Processes are remotely monitored through networks of smart devices. And every device represents a potential entry point for malicious intrusion – into the device itself, or onto the network to which it’s connected. These new security threats pose technology challenges in securing and stabilizing such large systems. In such an environment, root-of-trust (RoT) technology is becoming an essential requirement for every connected device.
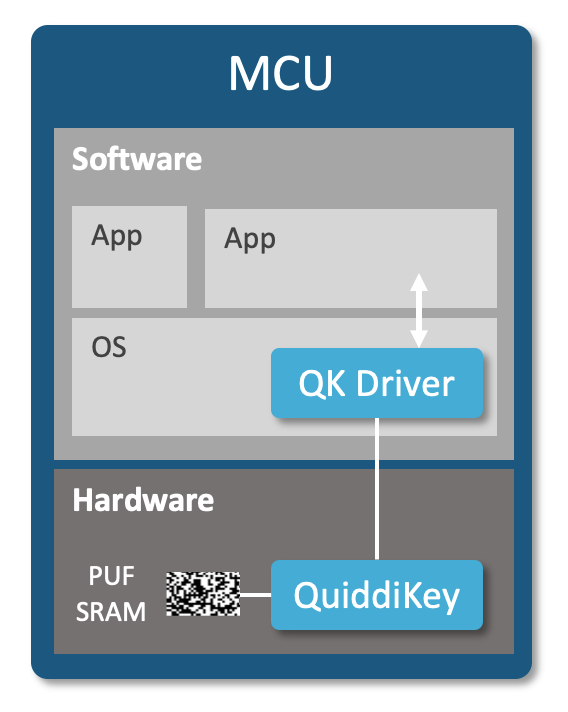
QuiddiKey® 100 is a physical unclonable function or PUF-based RoT solution that can be applied easily to almost any chip – even the tiniest microcontrollers – without the need for adding costly, security-dedicated silicon. QuiddiKey 100 can also be integrated as a trust anchor for other crypto libraries, extending the chain of trust beyond just a single device. QuiddiKey has been deployed and proven in hundreds of millions of devices certified by EMVCo, Visa, CC EAL6+, PSA, ioXt, and governments across the globe.

Features
- Uses standard SRAM start-up values as a PUF to create a hardware root of trust
- Offers key provisioning, wrapping, and unwrapping to enable secure key storage across the supply chain and for the lifetime of the device
- Eliminates target for physical attacks: root key is never stored, but re-created from the PUF each time it is needed
- Binds keys to the device so they can only be recreated and accessed on the device on which they have been created on
- Eases integration with custom driver API
Benefits
- Integrates easily and scales with all fabs and technology nodes
- Offers a higher level of security than traditional key storage in NVM such as secure flash, OTP or e-fuses
- Enables designers to create and store an unlimited number of keys securely in unprotected NVM on/off chip
- Minimizes overhead through optimized hardware design
- Eliminates the need for centralized key management and programming
- Remains secure post quantum computing
Why You Need QuiddiKey
Secure supply chain: Each QuiddiKey user can generate an unlimited number of device-unique keys. None of these keys are ever stored on the device. This means that each user in the supply chain can derive their own device-unique keys and import and protect other secrets, without these keys or secrets being known to the manufacturer or other supply-chain users. The wrapping functionality enables supply-chain applications and IP to be securely and reliably protected – for the lifetime of the device – prior to being deployed in the field.
Protection against reverse-engineering, counterfeiting/cloning: QuiddiKey protects firmware IP by encrypting it with a PUF-derived encryption key that is locked to the hardware instance of the device. If the firmware IP tied to a device with QuiddiKey is copied to other device instances, these rogue devices cannot unlock the IP or use it, because every device has a different hardware fingerprint.
Other use cases: Secure key storage, flexible key provisioning, HW-SW binding, secure communication, authentication
QuiddiKey 100 Configurations
QuiddiKey 100 is available in off-the-shelf configurations with size ranging between 39k and 64k gates. Configurations differ according to functionality, performance and compliance.
| QuiddiKey 100 v1.0 Configurations | |
|---|---|
| Generate device keys and random values | ✓ |
| Wrap and unwrap keys | (✓) |
| Size (k gates) | 39-64 |
| AC size (bytes) | 1000 |
| Security strength (bits) | 256 |
| Maximum key length (bits) | 4096 |
| Time to root key (k cycles) | 49-68 |
| SRAM required for PUF (kB) | 2-4 |
| Interface | APB |
| Logic BIST | (✓) |
| SRAM health checks | ✓ |
| SRAM anti-aging | ✓ |
| PUF monitoring | ✓ |
| Attack countermeasures | ✓ |
| NIST CAVP certification (DRBG, AES, KDF) | (✓) |
| NIST SP 800-90 compliant | (✓) |
(✓) features are optional
Operational Range
QuiddiKey has been embedded on MCU/SoC/ASICs in a diverse set of foundry/process node combinations. SRAM PUF responses have been qualified for use with QuiddiKey in a wide range of operational environments.

QuiddiKey 100 Deliverables

QuiddiKey 100 IP can be integrated easily into any semiconductor design across all foundries and process nodes. Standard deliverables include:
- RTL netlist (VHDL, Verilog)
- Testbench (UVM, VHDL), C model
- Synopsys Design Compiler® synthesis constraints (tcl)
- QuiddiKey driver (C sources, headers)
- QuiddiKey register description (IP-XACT)
- Datasheet, integration manual and driver documentation
- NIST documentation (SP 800-90A/B)
 Driver Eases Integration
Driver Eases Integration
The QuiddiKey 100 driver eases the use of the HW IP for developers in an embedded software environment. It is delivered as C source code and comes with a reference manual, integration tests and the QuiddiKey 100 register description.

 Driver Eases Integration
Driver Eases Integration You will be redirected to our new page on the Synopsys website in 15 seconds.
You will be redirected to our new page on the Synopsys website in 15 seconds.